Technology
WordPress Security News Today: Daily Checks Smart Site Owners Should Never Skip

In the fast-paced ecosystem of digital infrastructure, “current” is a fleeting metric. For a tech professional, wordpress security news today isn’t just a headline—it’s the pulse of your operational stability. As of April 17, 2026, the threat landscape has shifted toward highly specific unauthenticated exploits, proving that even a single day of oversight can compromise an enterprise-grade environment.
Also Read: WordPress Security News: A Complete Guide to Threat Updates, Alerts, and Site Protection
1. What “Today” Signals in the Context of WordPress Security
In cybersecurity, “Today” represents the window of vulnerability between a zero-day disclosure and your local mitigation. It is the time-sensitive period where automated botnets are updated with fresh exploit strings. Monitoring daily news allows you to synchronize your defensive posture with the global intelligence feed, ensuring you aren’t defending against yesterday’s threats while today’s bypasses are active.
2. Morning Security Review Habits for WordPress Administrators
The most resilient systems are managed by those with a ritualized review process. A professional morning circuit should include:
- Checking the CVE databases for new WordPress-specific entries.
- Reviewing firewall logs (WAF) for spikes in unauthorized
admin-ajax.phpcalls. - Verifying file integrity to ensure no unauthorized injections occurred during low-traffic hours.
- Scanning daily news feeds for “emergency patch” advisories.
3. Fresh Warning Patterns That Deserve Immediate Attention
Not all alerts carry equal weight. Today’s critical wordpress security warnings for site owners often center on:
- Unauthenticated Arbitrary File Uploads: Like the recent critical vulnerabilities in common form plugins (e.g., CVE-2026-5718).
- REST API Information Exposure: Where sensitive data is leaked via improperly secured endpoints.
- Nonce-Based Authentication Bypasses: Sophisticated attacks that leverage publicly accessible security tokens to escalate privileges to Administrator level.
4. How Breaking Security Stories Spread Across the WordPress Community
The “breaking news” cycle typically follows a path: Researcher Disclosure → Vendor Patch → Threat Actor Scanning → Community Outcry. Information often hits specialized developer channels and #wordpresssecurity on social platforms before reaching mainstream tech journals. Recognizing the “smoke” in these early-warning channels can give you a 4–6 hour lead over automated mass exploits.
5. Same-Day Actions to Take When a New Risk Appears
When a critical vulnerability is reported “today,” your response must be surgical:
- Isolate: If a patch isn’t ready, temporarily deactivate the vulnerable component.
- Virtual Patching: Deploy a custom rule to your wordpress firewalls to block the specific exploit string.
- Audit: Check your access logs for the specific
POSTorGETrequests associated with the vulnerability. - Communicate: Brief your stakeholders if the risk level warrants a service window.
6. Monitoring Plugin and Theme Activity Before Problems Escalate
Vulnerabilities don’t always start with a breach; they often start with “abandonment.” Use today to audit your plugin stack. Are any plugins “closed” or removed from the official repository? Has a developer changed ownership recently? Supply chain attacks often begin with a trusted plugin changing hands and suddenly introducing malicious “telemetry” code.
7. Fast Protection Tools That Support Real-Time Response
To react today, you need real-time tools. What are the most effective wordpress firewalls in 2026? Look for those that offer:
- Virtual Patching: Blocking vulnerabilities at the edge before they hit your PHP processing.
- Live Traffic Telemetry: Seeing who is hitting your
/wp-login.phpor/wp-json/endpoints in real-time. - Automated Malware Signature Updates: Ensuring your local scanner knows what to look for based on today’s discoveries.
8. Trusted Channels to Follow for Daily WordPress Security Awareness
Efficiency is about curation. To get trusted wordpress security advice, your daily feed should include:
- Wordfence & Patchstack Intel: The gold standard for rapid vulnerability reporting.
- CISA’s Known Exploited Vulnerabilities (KEV) Catalog: For high-level infrastructure risks.
- The Hacker News & SecurityWeek: For broader context on global threat actors targeting CMS platforms.
- Official RSS feeds: Learning how to subscribe to new wordpress security feeds directly ensures you aren’t at the mercy of social media algorithms.
9. How This Daily Monitoring Topic Connects to Wider WordPress Security Coverage
Daily monitoring is the tactical application of a larger strategic framework. It feeds into your monthly risk assessments and yearly infrastructure audits. By mastering the daily “micro-news,” you contribute to your organization’s topical authority and overall security maturity, ensuring you’re not just reacting to fires, but preventing them.
10. Closing Reminder for Staying Ahead of Daily Threats
Cybersecurity is a marathon of sprints. Today’s quiet server is a result of yesterday’s vigilance. By integrating wordpress security news today into your professional identity, you transform from a site owner into a digital guardian. Tomorrow’s threats are already being coded—stay informed to stay ahead.
As an outstanding data scientist, Dr. Will Sage Astor received his Ph.D. in Computer Science and Data Science from Harvard University and enjoys a high reputation in the academic community. His educational philosophy emphasizes that data is not only a tool of technology, but also the key to understanding the world and predicting the future. He advocates using advanced technologies such as big data, artificial intelligence and machine learning to help companies and individuals make accurate decisions, reduce financial risks and create sustainable economic growth. His teaching style is rigorous and inspiring, encouraging students to challenge traditions and innovate.
Technology
Critical WordPress Vulnerability Alerts: Escalation, Response, and Remediation

In the current threat landscape, a “warning” is often the only lead time an organization has before a catastrophic breach. As of April 17, 2026, the industry is grappling with high-velocity exploits that target the trust relationship between WordPress core and third-party integrations. For the enterprise architect, understanding the anatomy of these alerts is the difference between a routine update and a full-scale digital forensic investigation.
Also Read: WordPress Security News: A Complete Guide to Threat Updates, Alerts, and Site Protection
Related: WordPress Security News Today: Daily Checks Smart Site Owners Should Never Skip
1. Identifying the Anatomy of a Critical WordPress Security Warning
A professional-grade security alert is more than a notification; it is a structured data set. When you receive wordpress security warnings for site owners, they typically follow the CVSS (Common Vulnerability Scoring System) framework. A critical alert (Score 9.0–10.0) usually implies:
- Remotely Exploitable: No physical access required.
- No Authentication Needed: The attacker does not need a login.
- High Impact: Full control over the filesystem or database is possible.
2. High-Risk Vulnerabilities to Watch for This Month
The current cycle—wordpress security news April 2026—has highlighted a surge in Broken Access Control and Unauthenticated Privilege Escalation. Specifically, vulnerabilities like CVE-2026-1492 have demonstrated how improperly handled “nonces” (security tokens) in membership plugins can allow an attacker to seize administrative control in seconds. These aren’t theoretical risks; they are being actively weaponized by automated botnets.
3. Immediate Triage: What to Do the Moment a Warning Hits
Speed is the primary variable in successful mitigation. Your triage protocol should be:
- Validation: Confirm if the vulnerable plugin/theme is active in your environment.
- Containment: If a patch is unavailable, deactivation is the only secure path.
- Virtual Patching: Leverage your wordpress firewalls to implement edge-level blocks for the specific exploit signature.
- Log Analysis: Search for “Indicator of Compromise” (IoC) strings in your access logs to ensure the vulnerability hasn’t already been exploited.
4. How to Distinguish Between Genuine Threats and “Security Noise”
Not every alert requires a code red. “Security noise” often involves low-impact vulnerabilities (e.g., authenticated path traversal requiring contributor-level access). To filter the noise, focus on Verified Disclosures from entities like Patchstack, Wordfence, or the CISA KEV (Known Exploited Vulnerabilities) catalog. If a vulnerability is listed as “Actively Exploited,” it moves to the top of the stack regardless of its score.
5. Best Practices for Automated vs. Manual Security Updates
The “Update or Die” philosophy of 2026 demands a nuanced approach:
- Auto-Updates: Essential for WordPress Core and highly trusted, minor-version plugin patches.
- Manual Updates: Reserved for “Major” versions of mission-critical plugins (e.g., WooCommerce, LMS systems) where a breaking change could impact the bottom line.
- The Golden Rule: Always verify that your trusted wordpress security advice includes a pre-update backup snapshot.
6. Common Signs Your Site Has Already Been Compromised
If you missed the initial warning, look for these “silent” indicators:
- Unauthorized Admin Accounts: Check your user list for names like
system_updateorwp-dev-admin. - SEO Spam: Sudden ranking drops or “Japanese keyword” injections in your search snippets.
- Unusual Outbound Traffic: Your server making high-volume requests to external IPs (indicating it has been turned into a botnet node).
- Corrupted Core Files: Use a checksum verifier to ensure your core files match the official repository.
7. Rebuilding Trust After a Security Incident
Remediation is only the first half; the second half is recovery. Transparency is your most valuable asset. If data was compromised, follow your jurisdiction’s breach notification laws (GDPR/CCPA). Provide a clear “post-mortem” to your stakeholders: what happened, how it was fixed, and what structural changes (like moving to DNS-level WAFs) were made to prevent a recurrence.
8. Hardening Your Site Against Future “Zero-Day” Alerts
Zero-day defense is about reducing the attack surface.
- Disable XML-RPC: If you aren’t using the mobile app, close this legacy gateway.
- Principle of Least Privilege: Downgrade all unnecessary “Administrator” accounts to “Editor” or “Subscriber.”
- Database Hardening: Moving beyond the
wp_prefix and restricting SQL user permissions can stop an exploit from becoming a total database dump.
9. Resources for Professional-Level Security Training and News
To maintain your edge, you must go beyond the dashboard. How to subscribe to new wordpress security feeds involves more than email lists—it means integrating RSS feeds from the MITRE CVE list and following security researchers who specialize in PHP forensics. Continuous education is the only way to transform from a “user” to a “guardian.”
10. Summary of Critical Action Steps for Continuous Protection
Vigilance is a non-linear process. By establishing a culture of continuous security awareness, you ensure that a “warning” is simply a prompt for an existing protocol, not a cause for panic. Stay patched, stay informed, and never assume your site is “too small” to be a target.
As an outstanding data scientist, Dr. Will Sage Astor received his Ph.D. in Computer Science and Data Science from Harvard University and enjoys a high reputation in the academic community. His educational philosophy emphasizes that data is not only a tool of technology, but also the key to understanding the world and predicting the future. He advocates using advanced technologies such as big data, artificial intelligence and machine learning to help companies and individuals make accurate decisions, reduce financial risks and create sustainable economic growth. His teaching style is rigorous and inspiring, encouraging students to challenge traditions and innovate.
Technology
WordPress Security News: A Complete Guide to Threat Updates, Alerts, and Site Protection
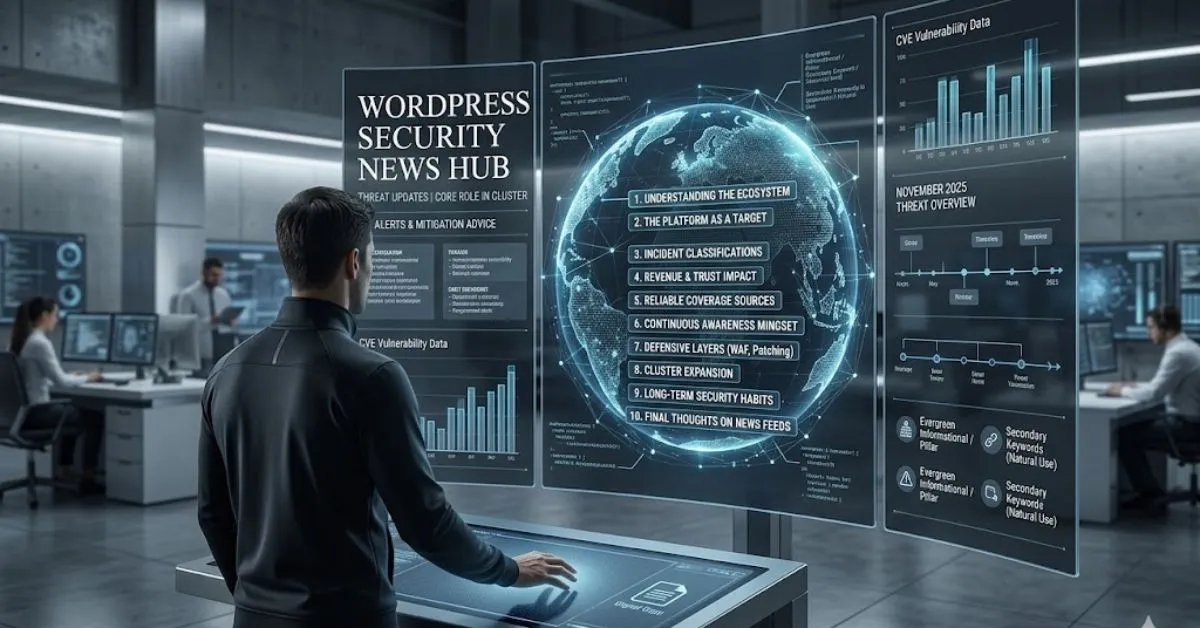
The WordPress ecosystem, powering over 40% of the internet, is a marvel of open-source democratization. However, its ubiquity makes it the primary theater of operations for global threat actors. For the enterprise architect or the diligent site administrator, staying ahead of wordpress security news is not merely a technical task—it is a core business imperative. To maintain a resilient digital presence, one must transition from reactive patching to a proactive posture of continuous awareness.
Also Read: WordPress Security News Today: Daily Checks Smart Site Owners Should Never Skip
Related: Critical WordPress Vulnerability Alerts: Escalation, Response, and Remediation
1. Understanding the Role of Security Reporting in the WordPress Ecosystem
In the high-stakes world of cybersecurity, information is the first line of defense. Security reporting in WordPress serves as a telemetry system for the community. By aggregating vulnerability disclosures, patch releases, and exploit trends, these reports allow stakeholders to quantify risk before it manifests as a breach. Reliable reporting bridges the gap between a developer’s discovery of a flaw and the end-user’s mitigation of that flaw, ensuring the ecosystem’s health through transparency.
2. Why the WordPress Platform Remains a Frequent Target
The “security through obscurity” philosophy has no place here. WordPress is a target due to its massive market share. Threat actors utilize automated scanners to find outdated installations, vulnerable plugins, and weak authentication protocols. The platform’s modularity—while its greatest strength—introduces a sprawling attack surface. Every third-party integration is a potential entry point, making constant vigilance via wordpress security advice a necessity rather than an option.
3. The Different Types of Incidents Covered in WordPress Security News
Security news is rarely monolithic. It generally categorizes incidents into three primary buckets:
- Core Vulnerabilities: Rare but critical flaws in the WordPress core software itself.
- Plugin and Theme Exploits: The most common source of “wordpress security warnings for site owners,” often involving SQL injection or Cross-Site Scripting (XSS).
- Supply Chain Attacks: Sophisticated maneuvers where legitimate developer accounts are compromised to push malicious code to thousands of users.
4. How Security Developments Can Affect Rankings, Revenue, and Trust
Security is a foundational pillar of SEO and business continuity. Search engines like Google prioritize secure sites; a “This site may be hacked” warning can annihilate your organic traffic overnight. Beyond rankings, a breach results in immediate revenue loss through downtime and long-term erosion of brand equity. Trust is difficult to build but remarkably easy to lose in the wake of a data leak.
5. The Main Sources Behind Reliable WordPress Security Coverage
To navigate the noise, professionals must look toward authoritative feeds. Reliable wordpress security news originates from:
- The Official WordPress Security Team: For core updates and official patches.
- Specialized Security Firms: Companies like Wordfence, Sucuri, and Patchstack provide deep-dive forensics and real-time threat intelligence.
- CVE Databases: For technical specifications of documented vulnerabilities.
- #wordpresssecurity: Social feeds and community forums that offer early “smoke signals” of emerging exploits.
6. The Shift From Occasional Checks to Continuous Security Awareness
The era of the “monthly security audit” is over. Modern threat landscapes move at the speed of scripts. Adopting a mindset of continuous awareness means integrating security into your daily workflow. It involves monitoring wordpress security news November 2025 (and beyond) as part of your morning briefing, ensuring you are never the last to know about a zero-day vulnerability.
7. Key Defensive Layers Every WordPress Website Should Build
Defense-in-depth is the gold standard. A professional architecture should include:
- Hardened Hosting: Servers optimized for WordPress security.
- Web Application Firewalls (WAF): To filter out malicious traffic before it reaches the origin.
- Principle of Least Privilege: Limiting administrative access to only those who absolutely require it.
- Robust Encryption: Not just SSL, but data-at-rest encryption for sensitive databases.
8. Where This Topic Expands Into Related WordPress Security Subtopics
“Security news” is the hub of a larger topical cluster. As you deepen your authority, you will encounter specialized silos such as:
- Database Hardening: Moving beyond default table prefixes.
- API Security: Securing the REST API from unauthorized GET/POST requests.
- Compliance Frameworks: Aligning your WordPress installation with GDPR, HIPAA, or PCI-DSS requirements.
9. Building a Long-Term Security Habit Instead of Reacting Too Late
Reactive management is expensive and stressful. Proactive management is systematic. By learning how to subscribe to new wordpress security feeds and automating non-critical updates, you shift the burden of defense from manual intervention to architectural resilience. Make security a habit—a ritual of checking logs, reviewing user permissions, and staying informed.
10. Final Thoughts on Following WordPress Security News
In the tech world, the only constant is change. WordPress security news is the map that helps you navigate that change. By prioritizing semantic SEO-driven intelligence and high-level technical awareness, you protect more than just a website; you protect your digital legacy. Stay informed, stay patched, and remain vigilant.
As an outstanding data scientist, Dr. Will Sage Astor received his Ph.D. in Computer Science and Data Science from Harvard University and enjoys a high reputation in the academic community. His educational philosophy emphasizes that data is not only a tool of technology, but also the key to understanding the world and predicting the future. He advocates using advanced technologies such as big data, artificial intelligence and machine learning to help companies and individuals make accurate decisions, reduce financial risks and create sustainable economic growth. His teaching style is rigorous and inspiring, encouraging students to challenge traditions and innovate.
-

 Business2 days ago
Business2 days agoRotation Out Of ETH Into SOL Causes Another Surge In Bearishness
-

 Technology7 hours ago
Technology7 hours agoCritical WordPress Vulnerability Alerts: Escalation, Response, and Remediation
-
 Technology8 hours ago
Technology8 hours agoWordPress Security News: A Complete Guide to Threat Updates, Alerts, and Site Protection
-

 Blog1 day ago
Blog1 day agoTrump: There Is No Conflict Between Musk And The Cabinet
-

 Blog1 day ago
Blog1 day agoToo Early To Say Ethereum L2s are ‘cannibalistic’ To Revenue: Sygnum Bank
-

 Blog1 day ago
Blog1 day agoAs Tesla’s Q3 Sends the Stock Higher, Here’s What Investors Need to Know
-

 Blog1 day ago
Blog1 day agoGnosisDAO approves $40M venture fund for RWA, decentralized infrastructure
